The Greek episode as a structural risk indicator
This essay answers the following question: What is the role and responsibilities of small and medium-sized allies in relation to modern military-industrial espionage?
Summary
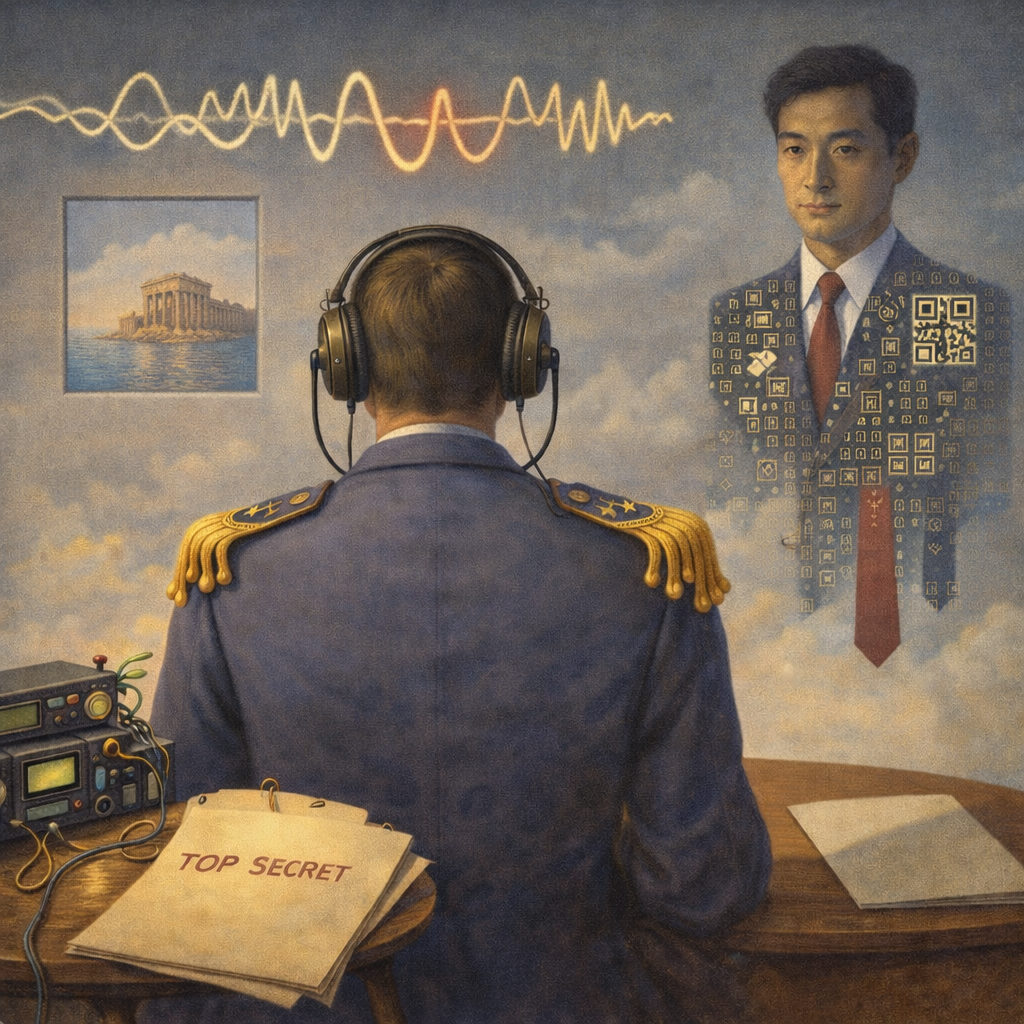
Military-industrial espionage has become a core mechanism of geopolitical competition. The Greek case of an air-force officer allegedly passing classified NATO planning to a Chinese entity illustrates how compromise at a peripheral node can open alliance-wide analytical windows. The essay explains the “mosaic” logic of intelligence: incremental collection of lower-tier fragments from multiple states and channels, then fusion into an operational picture of procedures, reaction times and dependencies. It argues that vague references to a “Chinese entity” reflect a hybrid ecosystem in which market actors and contractors interface with state direction, enabling plausible deniability and rapid innovation under civil-military fusion. Against a dual-use technology arms race, the theft of protocol and network details becomes strategically decisive because it can support disruption, spoofing and penetration of C4ISR—the integrated systems of command, control, communications, computers, intelligence, surveillance and reconnaissance. The essay concludes that medium allies such as Greece must treat counterintelligence, clearance governance and insider-threat monitoring as front-line contributions to collective security, not merely domestic compliance or criminal prosecution. in practice today.
Military-Industrial Espionage and the Greek NATO Case
Military-industrial espionage has become a core mechanism of contemporary geopolitical competition. The recent Greek case involving an air-force officer allegedly transferring classified NATO-related planning to a Chinese entity is emblematic of a broader structural shift in the global security environment. Such incidents no longer belong to the margins of intelligence activity; they reflect the centrality of information, networks, and technological access in modern power competition.
From “incident” to power architecture
The episode should not be treated as a minor curiosity or an isolated failure, but as part of a systemic web of military-industrial espionage that runs through the entire NATO ecosystem. The collection of information on communications protocols, command-and-control systems, and operational planning is not primarily about Greece as a national target. Rather, it concerns how China, Russia, and other actors attempt to read, model, and ultimately circumvent the Western architecture of power.
Greece, as a medium regional power and a gateway in the Eastern Mediterranean, is not targeted for its absolute strategic weight, but as a link in a larger chain. In intelligence terms, it represents a relatively vulnerable node within a much broader data-collection network that concerns the Alliance as a whole. A single wing commander with access to classified NATO information can therefore become a strategic force multiplier for a third power, because compromise at a peripheral node can open analytical windows into alliance-wide patterns of readiness, doctrine, procedures, and decision-making.
The “mosaic” logic of contemporary intelligence
The frequently posed question—“what can China gain from one small NATO state?”—overlooks the logic of modern intelligence collection, which resembles a mosaic rather than the pursuit of a single “smoking-gun” document. Chinese practice, as documented in numerous cases of industrial espionage and cyber-espionage, relies on the incremental acquisition of lower-tier information from multiple countries, institutions, and channels. These fragments are then analytically fused into a highly accurate operational picture of the adversary.
This approach offers clear advantages. It reduces operational risk by avoiding spectacular and easily attributable breaches of hardened central targets. It complicates counterintelligence, which traditionally prioritises major headquarters and core systems while underestimating peripheral environments. It also enables the use of commercial, semi-private, or contracting entities—such as cybersecurity firms, software vendors, and systems integrators—as intermediaries, blurring the boundary between state and private actors and diffusing responsibility.
In the Greek case, allegations concerning the use of specialised encryption software and the gradual exfiltration of documents related to Air Force operations and NATO planning are consistent with this low-visibility, mosaic-type method. The objective is not necessarily a single decisive secret, but the accumulation of sufficient fragments to map alliance procedures, reaction times, and technical dependencies.
The “Chinese entity”: state, market, or hybrid actor
The use of vague labels such as “foreign entity” or “Chinese entity”, rather than explicit references to the People’s Liberation Army (PLA—the armed forces of the People’s Republic of China) or to formal intelligence services, is analytically meaningful. It reflects the structural ambiguity of China’s intelligence ecosystem, in which cybersecurity companies, data brokers, and private contractors are connected to state structures through opaque contracts, party-state ties, and legal obligations to cooperate with public-security and military authorities.
Leaked internal files from Chinese cybersecurity firms in recent years have revealed precisely such a marketplace for espionage services, where commercial vendors sell access to foreign government and military data to public-security organs and defence clients. For Beijing, reliance on these intermediaries serves two strategic purposes: it preserves plausible deniability in the event of exposure, and it harnesses market-driven innovation as part of a broader military-commercial complex built around civil-military fusion.
The Greek affair, with the likely involvement of software or communications companies operating through subsidiaries in Western jurisdictions, fits this hybrid pattern. In such cases, the handler may not even be a Chinese national, but rather a node within a transnational corporate web. From a NATO perspective, the “Chinese entity” receiving Greek-origin data is therefore best understood not as a standalone actor, but as one component of a state-directed, commercially enabled ecosystem of espionage and influence that systematically targets the Alliance.
The geopolitical economy of military-industrial espionage
These dynamics unfold against the backdrop of a new arms race in dual-use technologies—artificial intelligence, advanced semiconductors, space-based systems, and cyber tools—where the line between civilian and military, market and defence, has largely disappeared. The United States, the European Union, and key allies have adopted strict export controls on advanced technologies to China precisely because the risk of “leakage” through commercial channels is now understood as a strategic-level threat rather than a marginal trade issue.
This perception is crystallised in the 2022 NATO Strategic Concept adopted at the Madrid Summit, which states that “China’s stated ambitions and coercive policies challenge our interests, security and values”, and identifies the People’s Republic of China (PRC—the official name of the Chinese state) as a “systemic challenge” to the Alliance. The document highlights, among other factors, China’s civil-military fusion strategy and its activities in space, cyberspace, and disinformation—domains in which industrial, technological, and military logics are tightly interwoven. In this context, industrial espionage is not merely illicit access to intellectual property, but a tool for accelerating military modernisation at lower cost and shorter time horizons. For China, insight into NATO communications protocols and command structures enables the design of jamming, spoofing, or penetration tools that can be embedded in its own C4ISR systems—that is, systems for Command, Control, Communications, Computers, Intelligence, Surveillance, and Reconnaissance, which together constitute the digital nervous system of modern armed forces.
C4ISR vulnerabilities and alliance networks
Understanding why apparently technical details matter requires conceptual clarity. “C4I” refers to the integrated framework of Command, Control, Communications, Computers, and Intelligence that allows a military organisation to exercise effective operational command. “C4ISR” extends this framework by incorporating Surveillance and Reconnaissance, covering the full cycle of sensing, processing, and acting on information from the tactical to the strategic level.
NATO and national C4ISR architectures combine communications networks, cryptographic protocols, command-and-control software, and sensor systems to provide real-time situational awareness and coordinated decision-making. Analyses of future warfare consistently emphasise that blinding, manipulating, or corrupting these networks—by breaking encryption, deceiving sensors, or interfering with data flows—can induce strategic paralysis, misdirected orders, and heightened risk of operational failure. Under these conditions, the theft of seemingly technical documents on protocols or network architectures amounts to a direct attack on the Alliance’s operational brain.
For small and medium-sized allies such as Greece, participation in advanced alliance networks brings significant security benefits, but also increases their value as targets for military-industrial espionage. Their national security apparatus must therefore operate not only as a guardian of national secrets, but as a frontline defender of allied technological superiority, since compromise at a single weak link can reverberate across the entire C4ISR web.
Clearances, counterintelligence, and institutional resilience
The clearance issue in the Greek case exposes a deeper institutional challenge: the capacity of medium powers to manage access to increasingly complex systems of classified information-sharing. From recruitment and vetting to periodic re-evaluation, gaps in monitoring the financial, social, and digital vulnerabilities of senior personnel create favourable conditions for recruitment by foreign intelligence services or their proxies. In Greece, the months-long surveillance operation that preceded the arrest raises two legitimate policy questions: how long the officer retained meaningful access to sensitive data before detection, and whether such access created opportunities for further compromise within the system. In practical terms, this underscores the need for mandatory periodic re-vetting of personnel with access to alliance-level data, the adoption of continuous evaluation mechanisms integrating financial, digital, and behavioural indicators, and the harmonisation of minimum insider-threat standards across NATO members.
If such cases are reduced to domestic political point-scoring, the underlying security failure risks being politicised away rather than addressed through institutional reform proportional to the threats identified in NATO’s own assessments of hybrid and cyber activity. From the Greek episode to the strategic landscape
Strategically, the Greek case fits a broader pattern of growing Western concern over the scale and sophistication of Chinese cyber- and industrial-espionage operations targeting NATO members. NATO’s public Cyber Defence policy explicitly notes that China’s malign hybrid and cyber activities, as well as its disinformation efforts, target Allies and harm the Alliance’s security, placing the PRC among the sources of substantial and persistent cyber threats to democratic systems and critical infrastructure.
During the Washington Summit, allied leaders and commentators underscored that the Alliance is now openly criticising Chinese cyber-espionage and its implications for global security, even as member states remain economically interdependent with Beijing. Complementary threat assessments indicate that while Russian state-sponsored actors often pursue more focused and destructive operations, Chinese cyber actors are more likely to engage in opportunistic intrusions aimed at extracting insight into alliance policies and future planning—an approach fully consistent with the mosaic intelligence logic described above.
For Greece, the stakes extend well beyond criminal prosecution. They include upgrading national counterintelligence to operate in a military-industrial, data-driven environment; redefining the relationship between political authorities, armed forces, and the defence industry through the lens of cybersecurity and information protection; and consolidating Greece’s role as a credible custodian of allied secrets at a time when technology transforms every medium-sized ally into a potential strategic vulnerability within the wider Alliance.
Policy takeaway
As power competition increasingly revolves around data, networks, and technological access, NATO’s collective resilience will depend less on the strength of its core and more on the institutional robustness of its peripheral nodes; treating clearance governance, insider-threat monitoring, and counterintelligence capacity in medium allies as integral elements of collective defence is therefore a strategic necessity rather than a domestic administrative concern.